Intro
We’re excited to introduce a new Fungible Token Contract, currently released in beta. This new configurable contract simplifies token deployments, reduces the number of account updates needed for common actions, and lays the groundwork for powerful customizations while preserving properties like a static verification key, which is required for cross-application compatibility.
Motivation
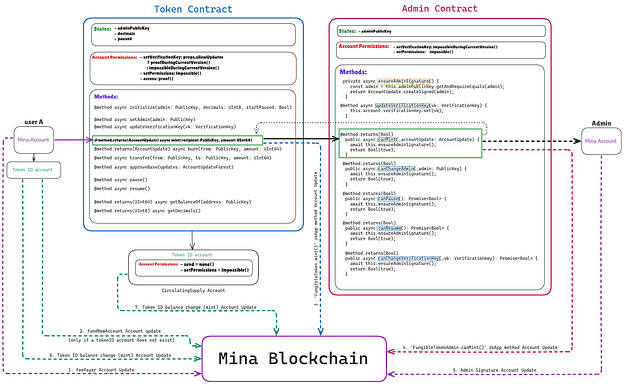
The original token standard relied on both a FungibleToken and a FungibleTokenAdmin contract. This added complexity, complicated deployments, increased account updates, and introduced trust assumptions around the admin.
The new design addresses these issues by:
-
Using a single contract with built-in configurability
-
Preserving a static verification key for auditability and composability
-
Supporting flexible logic via sideloaded proofs
This makes it easier to reason about token behavior while enabling more advanced use cases like gated minting and ZK-powered airdrops.
Key Features
Single Contract Design
Combines token and admin functionality, eliminating the need for an external admin contract. This reduces one account update per method (e.g. mint) and simplifies deployment.
Sideloaded Proof Support
Advanced conditions (e.g. “only mint if the user owns 1,000 MINA”) can be enforced using proofs that live outside the token contract. These do not alter the token’s verification key and support privacy-preserving logic.
Static Verification Key
All logic lives in a single, auditable contract.
Design of the current Fungible Token Standard (mint)
Account Updates for mint (7 total):
- feePayor
- fundNewAccount - only if a tokenID account does not exist
- FungibleToken.mint() zkApp method
- FungibleTokenAdmin.canMint() zkApp method
- Admin Signature
- Token ID balance change
- Token ID balance change
Design of new Fungible Token Contract (mint)
Account Updates for mint (6 total):
- feePayer
- fundNewAccount - only if a tokenID account does not exist
- FungibleToken.mint() zkApp method
- Admin Signature
- Token ID balance change (mint)
- Token ID balance change (mint)
Conclusion
The new Mina Fungible Token Contract is a cleaner, more composable foundation for token-based apps. It preserves auditability with a static verification key, reduces deployment overhead, and enables advanced features like privacy-preserving mint conditions with a single contract.
We invite developers to contribute and collaborate with us as we build on this foundation and evolve the contract together in the future. If you’re building zkApps that involve tokens, we encourage you to try it and let us know what you need next.